05 — The service layer
See it in action
KYA ships two dashboards: the Console for institutions managing their agent fleet, and the Operator Dashboard for network administrators overseeing the verification infrastructure. Both are production-ready, role-authenticated, and designed for institutional workflows.
 Console
Console
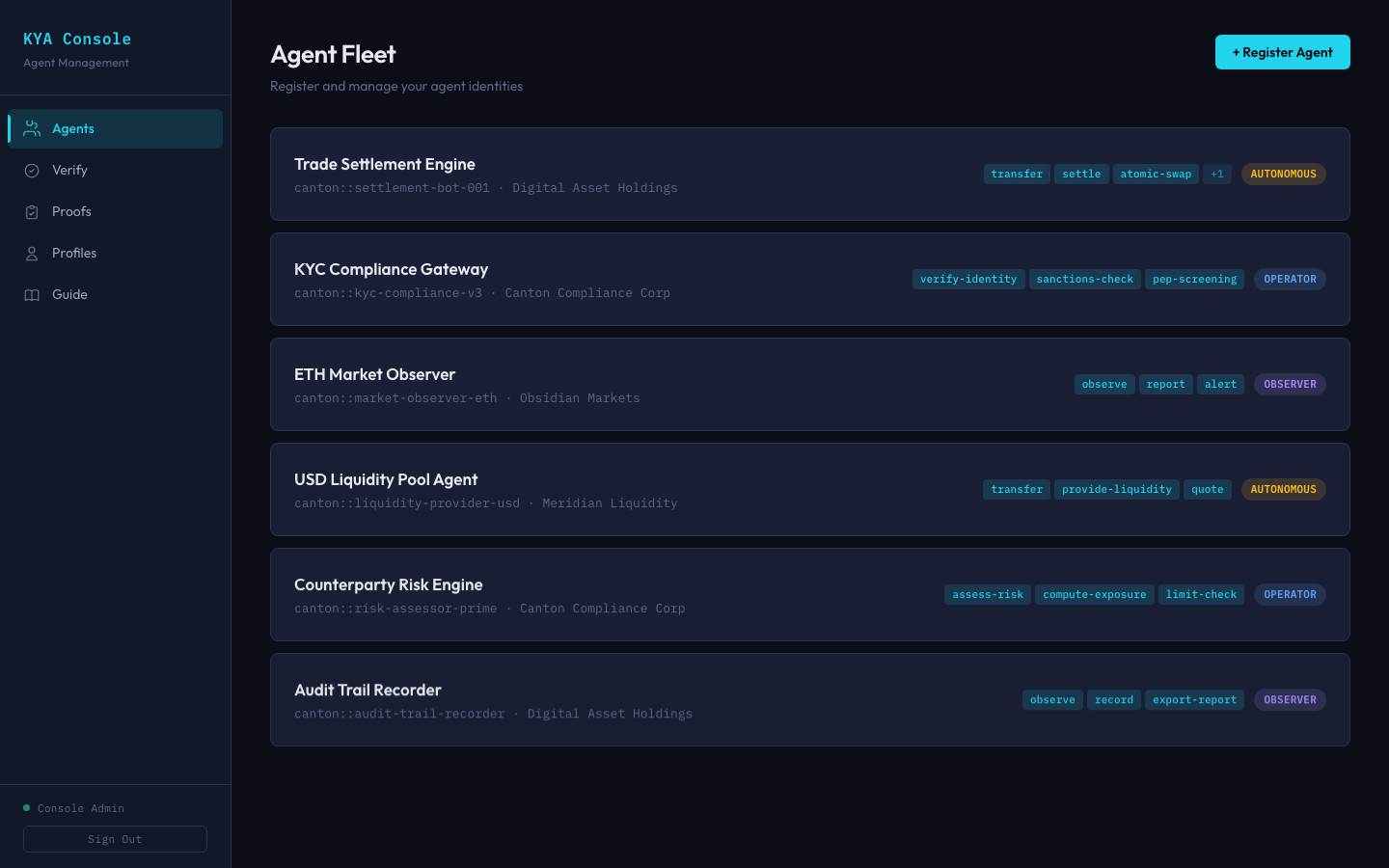
Agent Registry
Register and manage your agent fleet
Every AI agent operating on Canton gets a registered identity. The Agent Fleet view shows each agent's principal organization, class (autonomous, operator, or observer), and declared capabilities.
Institutions register agents here before deploying them. The capability badges act as the machine-readable permissions that counterparties verify during transactions.
 Console
Console
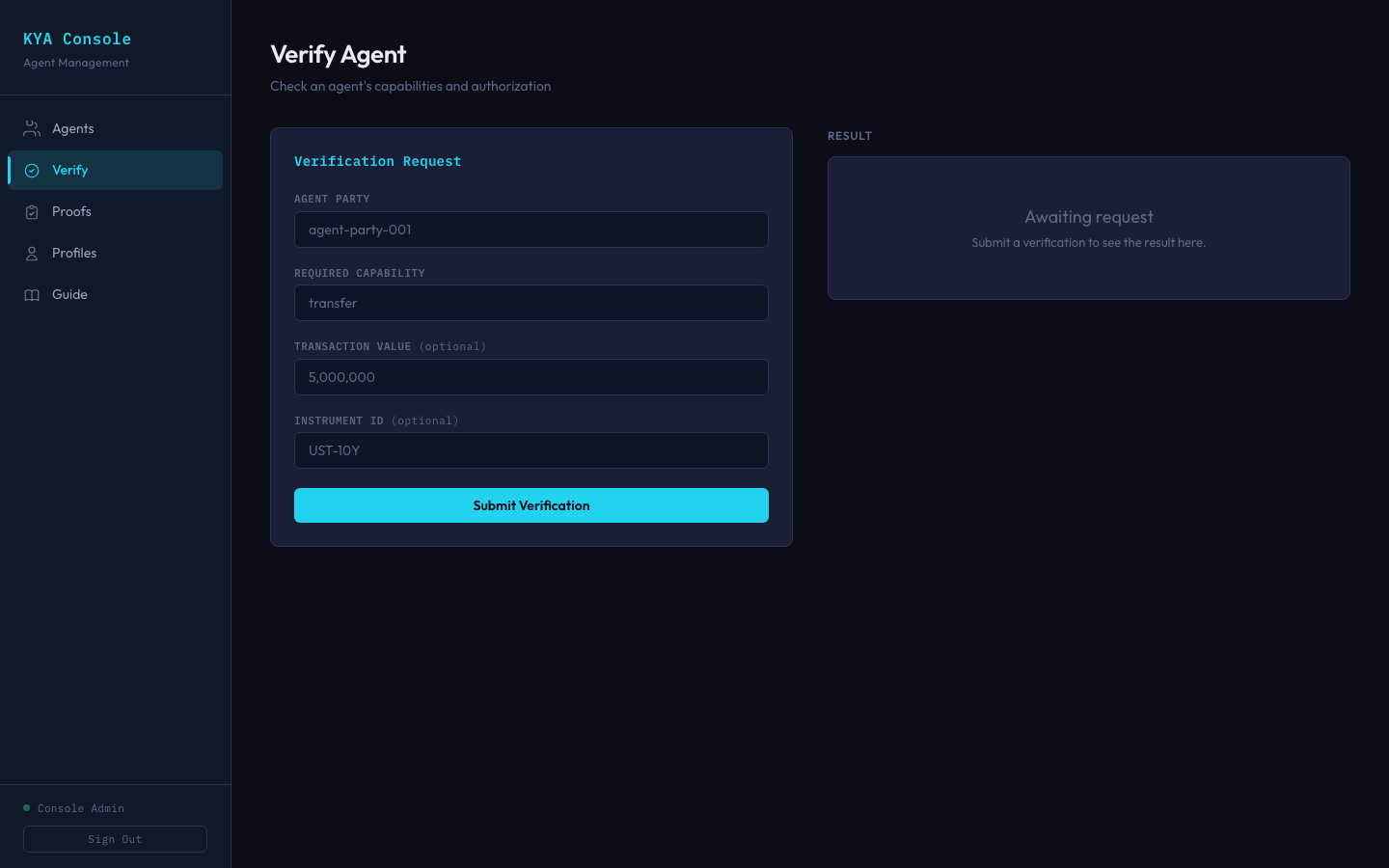
Verification
Verify an agent before transacting
Before accepting a trade, settlement, or collateral move from an agent, counterparties can verify its authorization. Specify the agent party, required capability, transaction value, and instrument.
KYA checks the delegation chain, validates limits, runs compliance hooks, and returns a cryptographic proof contract that the settlement workflow consumes.
 Console
Console
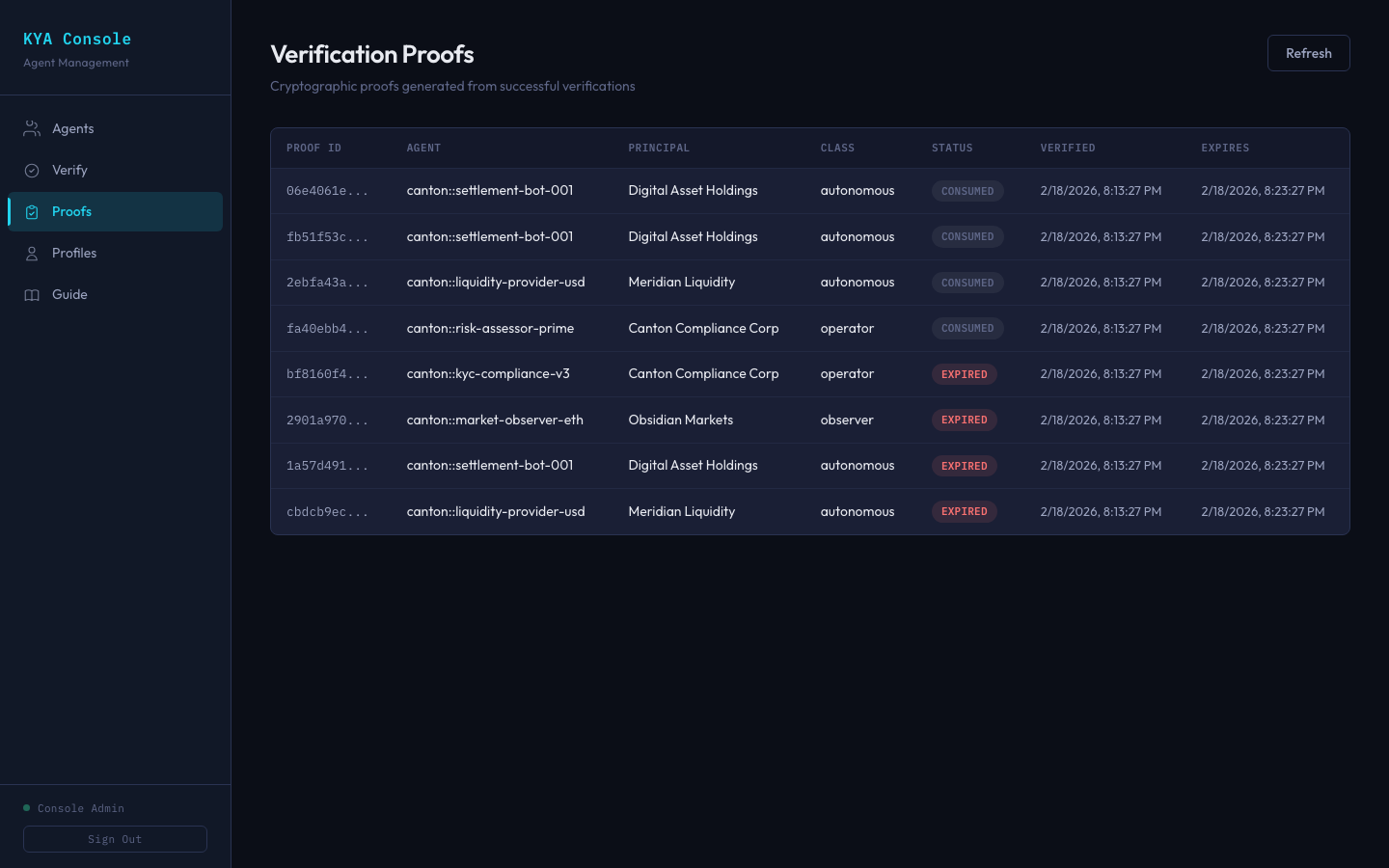
Proof Ledger
Cryptographic proofs for every verification
Each successful verification creates an on-ledger proof contract with an expiration window. Proofs start as Active and transition to Consumed when used in a settlement, creating a tamper-proof audit trail.
 Console
Console
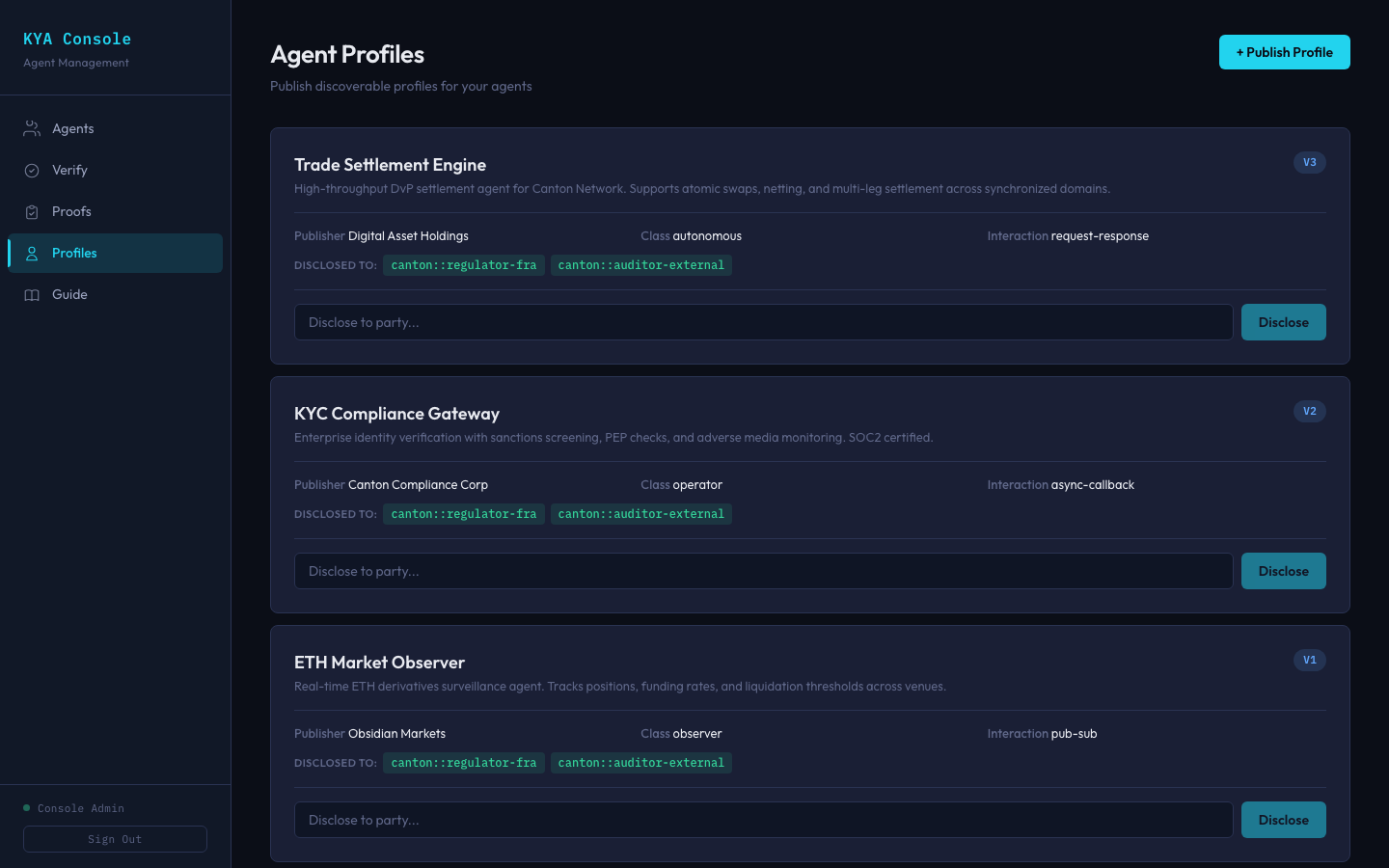
Agent Discovery
Publish profiles, control who sees them
Agent Profiles are a permissioned directory. Institutions publish versioned profiles describing what their agents do, then selectively disclose them to specific counterparties — regulators, auditors, or trading partners.
Unlike a public registry, nothing is visible until explicitly shared. Canton's Explicit Disclosure ensures profiles are cryptographically verified and unforgeable.
 Operator
Operator
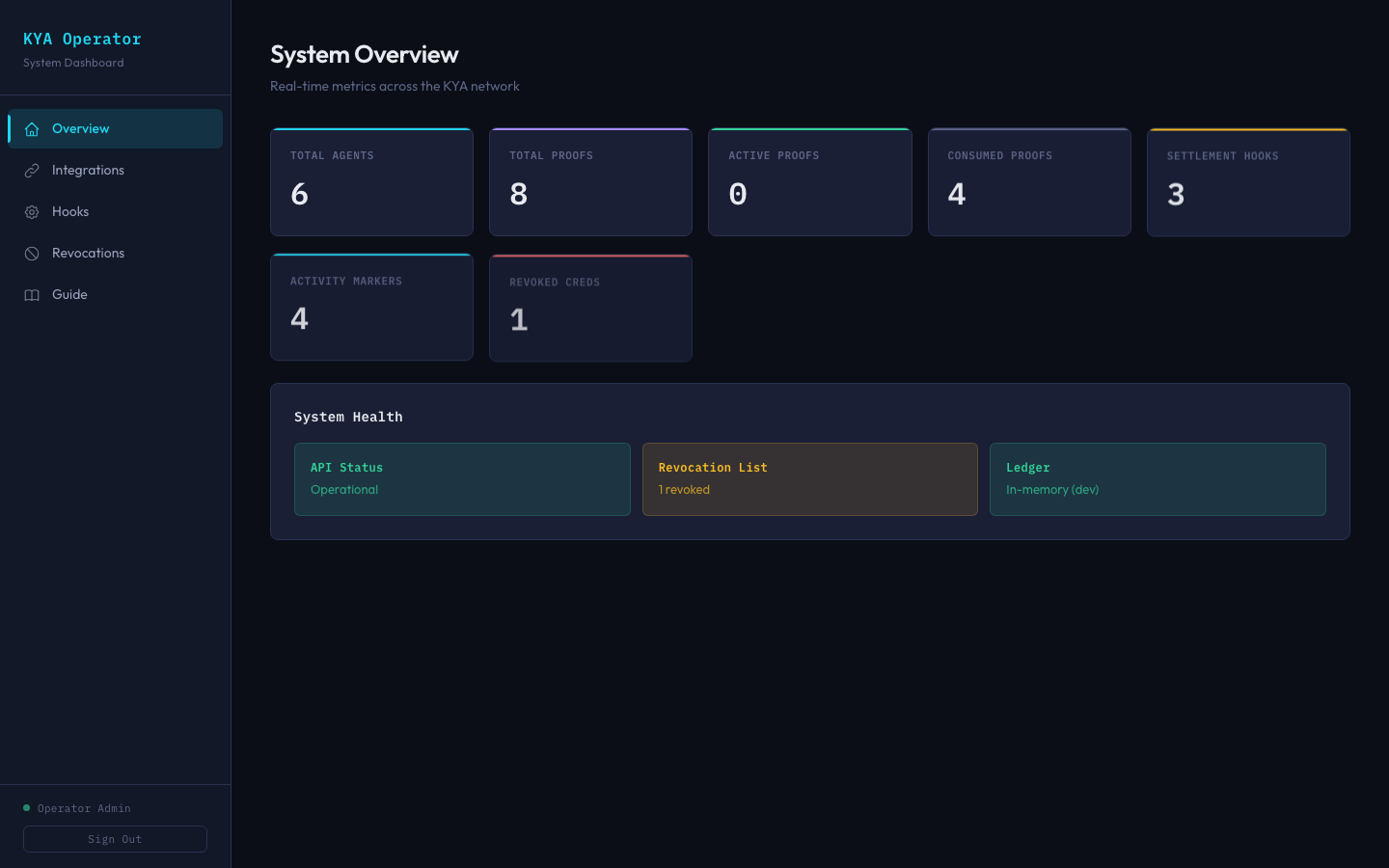
System Overview
Real-time metrics across the KYA network
The Operator Dashboard provides a live view of the verification infrastructure: total registered agents, active and consumed proofs, settlement hook activity, and credential revocation status.
System Health monitoring tracks API status, the revocation registry, and ledger connectivity — giving operators confidence the verification layer is functioning correctly.
 Operator
Operator
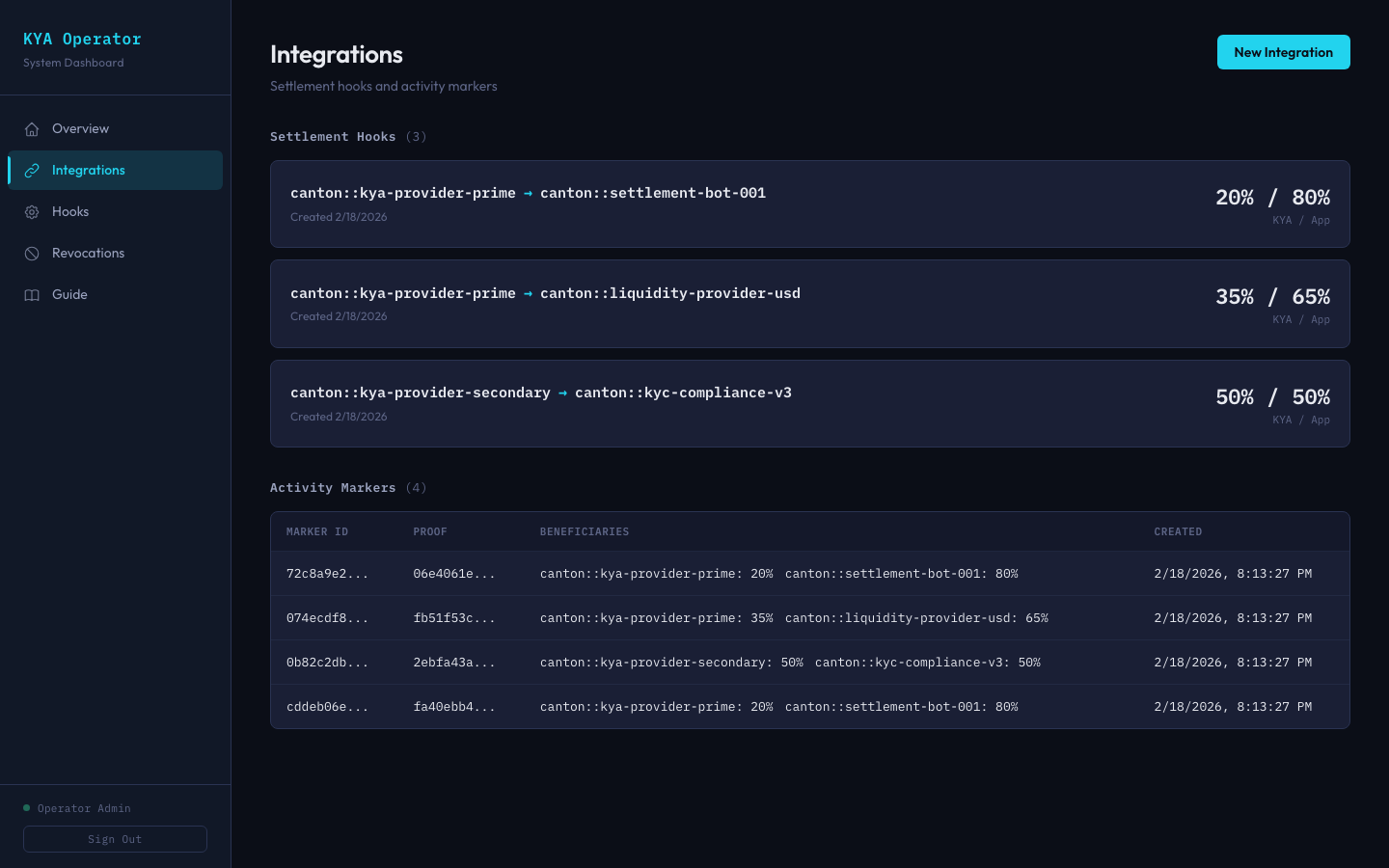
Integrations
Settlement hooks and reward sharing
Settlement Hooks connect KYA providers with integrating applications, defining how Canton Featured App rewards are split. Each hook visualizes the provider-to-app route and the reward percentage split.
Activity Markers create an immutable log of every settlement that consumed a verification proof, tracking beneficiaries and their reward weights for transparent compensation.
 Operator
Operator
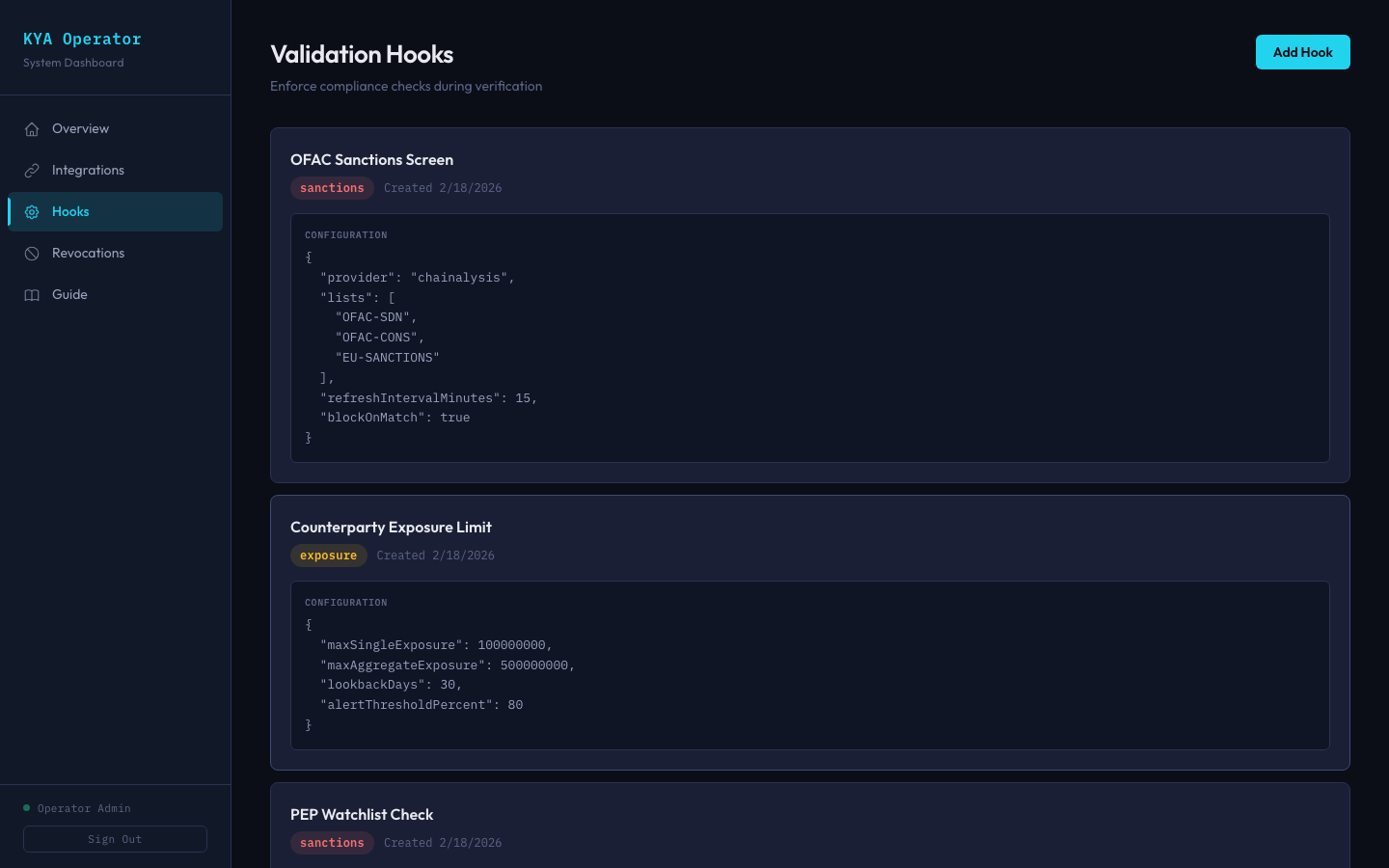
Compliance
Pluggable compliance checks at verification time
Validation Hooks run before any verification proof is issued. Configure sanctions screening against OFAC, EU, and PEP watchlists. Set counterparty exposure limits with aggregate thresholds and lookback windows.